SAC2020 Conference
Cyberweb - Oct 19-23, 2020
Program Committee
Accepted Papers
Registration
Program
Summer School
Call for Papers
Paper Submission
Previous SACs
Program
The full program is held on ResearchSeminars.org which allows you to change the date/time to your local time zone.
For each topic, you can find the links to the Zulip stream, the preproceedings of the PDF, and the recorded video:
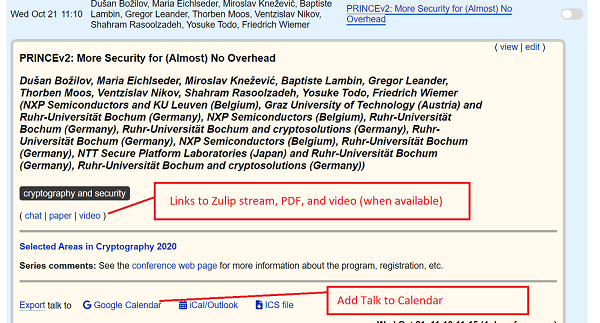
You can find copies of the preprint and video links on the List of Accepted Papers page too.
Zoom Session
The Zoom Session for talks (separate from summer school) is available at the following link:
- https://ucalgary.zoom.us/j/91523488202
- Meeting ID: 915 2348 8202
NB: The meeting is password protected to registered attendees. You will receive an email with the password.
Time Zone
The majority of the event is designed to be held roughly in “Atlantic Canada” time zone, however some sessions are in Asia/Oceania-friendly time-zone. You’ll notice thus a few large gaps in the program, that are not mistakes.
Invited Talks
Invited Talk #1: Trustless groups of unknown order
Benjamin Smith, INRIA and École Polytechnique
Groups of unknown order have cryptographic applications including time-lock puzzles, verifiable delay functions, and accumulators. While a trusted authority might simply choose an RSA group and be done with it, in the trustless setting the problem of generating cryptographically secure unknown-order groups is much more subtle. We will explore this problem, comparing two concrete constructions - class groups of quadratic imaginary fields, and Jacobians of hyperelliptic curves - with a special focus on the surprisingly complicated issues of security levels and appropriate key sizes.
About the Speaker
Benjamin Smith is a research scientist with INRIA, the French national computer science research institute, and an adjunct professor at École Polytechnique. His research is focused on number-theoretic cryptographic algorithms, especially in (hyper)elliptic curve cryptography and isogeny based cryptography.
Invited Talk #2: What’s so hard about Internet voting?
Vanessa Teague, Thinking Cybersecurity and Australian National University
The first papers about electronic voting were written only a year or two after the invention of public key cryptography. It all seemed so simple: some voting codes, a mixnet or two, and we could have private and verifiable remote voting for everyone.
But the more we think about elections as a specific engineering problem, the more subtle problems appear. How do we ensure that people can’t sell their votes or be coerced into voting in a particular way? What if the voter’s computer sends a different vote from the one the voter wanted? How can independent auditors test for mistakes or manipulation? If the protocol assumes a separation of powers or a distribution of trust, how do we make those independence assumptions true in practice? What if we discover after the election that there was a bug in the maths?
I’ll survey the history of good ideas in the literature, and explain why recent examinations of real systems have identified problems that researchers didn’t even consider.
We’re learning something about democracy and security as we go, but unfortunately we’re mostly learning about the fragility of our democratic systems and the limitations of our clever cryptographic solutions.
I’ll conclude with some positive developments, including Risk-Limiting Audits and pollsite e-voting systems, and why I think those directions are more promising than paperless Internet voting.
About the Speaker
Vanessa Teague is the CEO of Thinking Cybersecurity and Associate Prof (Adj.) in the Research School of Computer Science at the Australian National University. Her research focuses primarily on cryptographic methods for achieving security and privacy, particularly for issues of public interest such as election integrity and the protection of government data. She was part of the team (with Chris Culnane and Ben Rubinstein) who discovered the easy re-identification of doctors and patients in the Medicare/PBS open dataset released by the Australian Department of Health. She has co-designed numerous protocols for improved election integrity in e-voting systems, and co-discovered serious weaknesses in the cryptography of deployed e-voting systems in New South Wales, Western Australia and Switzerland. She lives and works on Wurundjeri land in Southeastern Australia (near Melbourne).
List of Accepted Papers
See List of Accepted Papers for all papers that will be in the program.